VectorThe Security Gateway for AI Agents & MCP
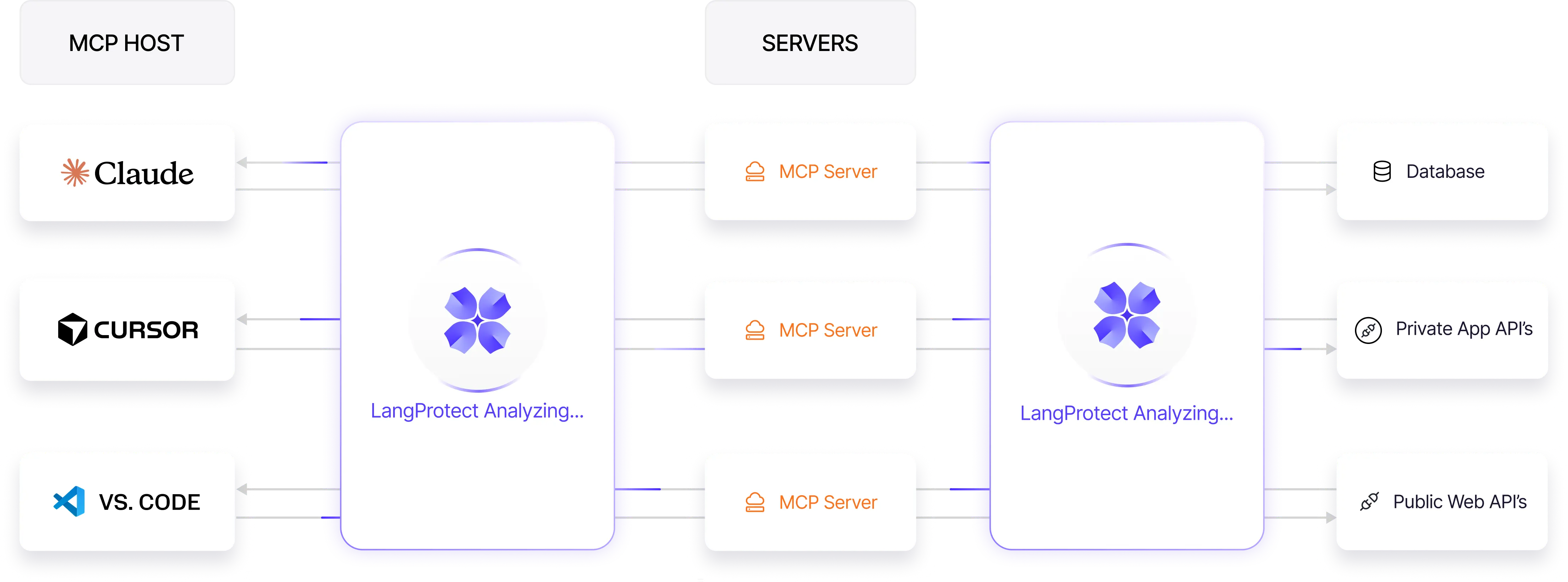
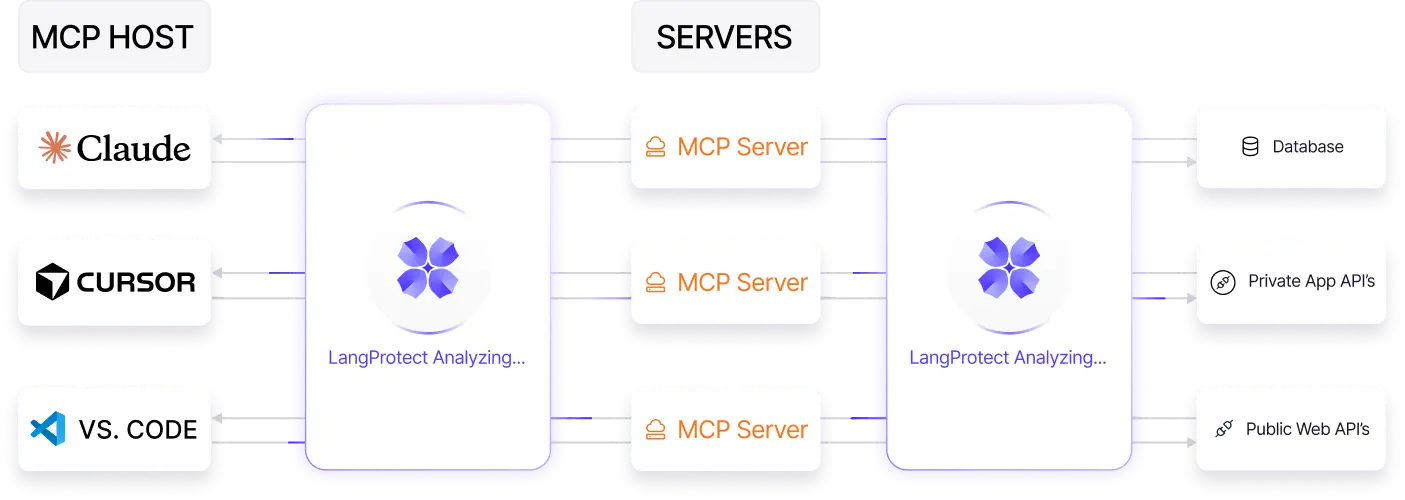
AI Agents now browse the web and access tools using MCP. LangProtect Vector provides the security layer you need to monitor these agents in real-time. We ensure every agent behaves, stays authorized, and never leaks sensitive data.
Why AI Agents & MCP Need a Secure Gateway
AI applications introduce a new execution layer where traditional controls have limited visibility. Guardrails must operate at runtime, when prompts, context, and outputs interact with real data and real systems.


Actions Can't Be Predicted
AI Agents are autonomous. Unlike a static button on a website, an agent's actions are generated on the fly. You cannot pre-approve every step, making real-time monitoring the only way to stay safe.
Data Can Be Siphoned
Once an agent connects to your internal systems via MCP, it has the power to read and summarize vast amounts of data. Without a gateway, there is nothing to stop an agent from accidentally sharing sensitive secrets with an external model.
Intent Can Be Manipulated
Malicious users (or even external websites the agent visits) can use "Indirect Prompt Injection" to trick your agent into thinking its new mission is to steal data or delete records.

The Open Door of MCP
The Model Context Protocol (MCP) is a powerful bridge to your data, but it is often unsecured. Without a dedicated security layer, any agent connected to the bridge can cross into your private databases.
Execution Happens in Stealth
Most agentic actions happen in the "background" without a human watching. If an agent performs an unauthorized task (like sending a phishing email), you may not find out until the damage is already done.
Over-Privileged Tool Access
Agents are often given "full access" to APIs and tools to make development easier. This "all-or-nothing" approach is a massive security hole that requires granular, tool-level permissions.
How Vector Secures the Agentic Workflow
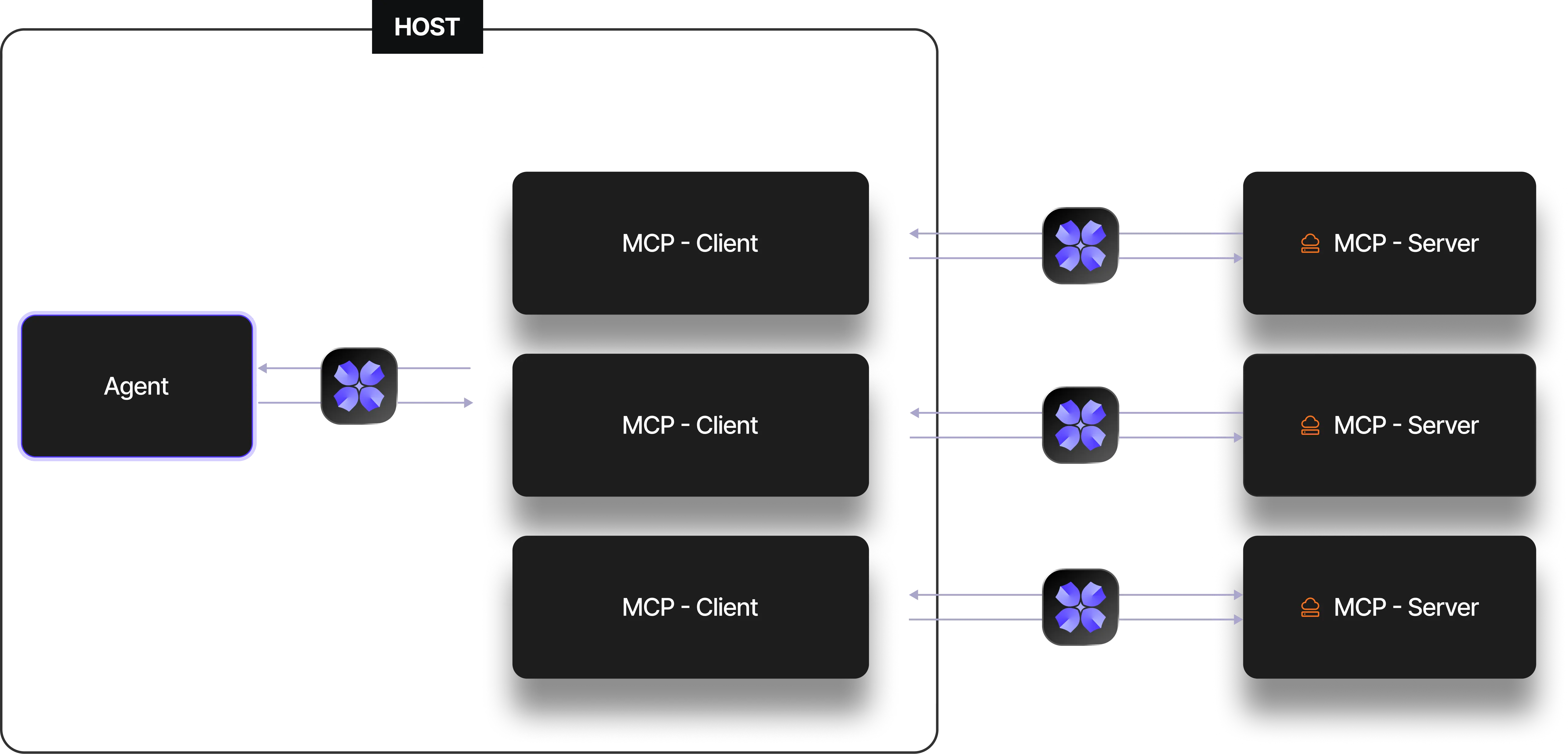
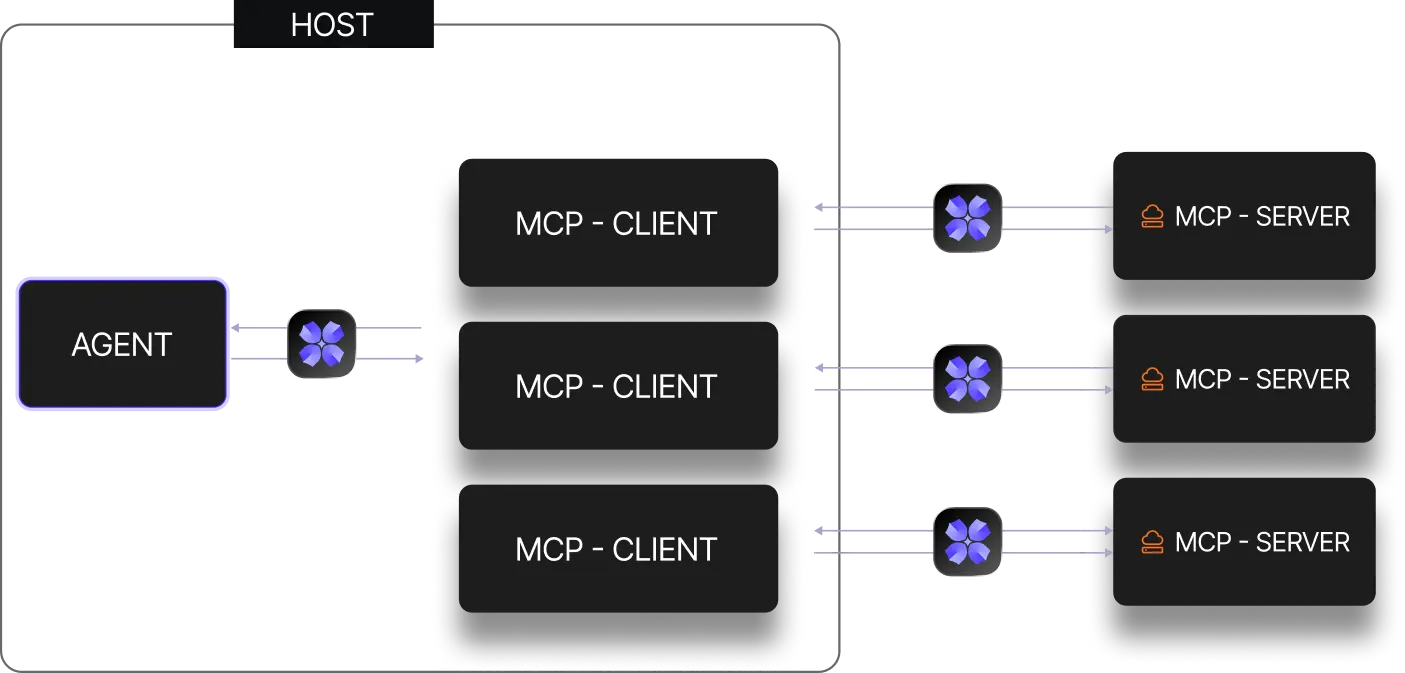
Vector enforces security at the exact moment of execution, before an agent's request ever touches your tools or data.

Intercept the Action Request
Vector sits inline between the AI Agent and the MCP server. It captures every intent, tool call, and resource request as they happen.

Evaluate Intent & Context
We don't just look for bad words. We analyze the reason behind the agent's request: "Is this specific agent supposed to be accessing this specific database right now?"

Apply the Kill Switch or Filter
Based on your company policy, Vector instantly decides to Allow, Block, or Redact. If an agent attempts a dangerous action, Vector prevents it from executing.

Record Every Move
Every decision is logged in a human-readable audit trail. You can see exactly what the agent tried to do, why Vector allowed or blocked it, and which policy was triggered.
What Vector Protects Against
AI Agents introduce a new Action Layer where traditional security is blind. Vector provides the guardrails and visibility needed to move from simple chat to autonomous execution safely.



Indirect Prompt Injections
Prevent poisoned data from external websites or documents from hijacking your agent's instructions. Vector identifies hidden malicious commands that try to force your agent into unauthorized behaviors.

Over-Privileged Tool Access
Stop the "all-access" security hole. Vector enforces the Principle of Least Privilege, ensuring agents only access the specific APIs, tools, and databases required for their immediate task.

Sensitive Data Exfiltration
Keep company secrets private. Vector monitors every data flow in real-time, redacting PII, credentials, and internal trade secrets before an agent can "siphon" them to an external LLM or third-party service.

Unauthorized Autonomous Actions
Prevent Rogue agent behavior. Whether it's an accidental database deletion or an unauthorized mass email, Vector acts as a Kill Switch that blocks harmful actions before they are executed.

Unsecured MCP Connections
Secure the Bridge between your models and your data. Vector monitors the Model Context Protocol (MCP) handshake to ensure no malicious resource requests are passed through the gateway.

Shadow Agent Discovery
Eliminate blind spots. Vector automatically discovers and inventories every AI agent and local MCP server running inside your corporate network, giving you 100% visibility into unmanaged AI.
Built for Enterprise Agent Governance
Vector is designed to fit seamlessly into high-security enterprise environments, giving security teams the visibility, control, and auditability they need to scale autonomous AI agents and MCP workflows safely.
Centralized Agent Control
Define and manage security policies for all your AI agents and MCP servers in one dashboard. Apply consistent guardrails across your entire agentic ecosystem instantly.
Role-Aware Access (RBAC)
Limit which agents can access specific tools or databases based on their assigned role. Ensure that a "Marketing Agent" can never access "Financial Data" via an MCP connection.
Human-Readable Audit Logs
Maintain a structured record of every action your agents take. We translate complex API calls into plain English, so you can easily see what was allowed, blocked, or redacted.
Real-Time Policy Enforcement
Vector scans the intent of every request in milliseconds. Our high-performance gateway ensures that security never slows down the execution speed of your autonomous workflows.
Automated MCP Discovery
Instantly find every "Shadow" agent and unmanaged MCP server running in your network. Get full visibility into how many AI agents are active and what systems they are touching.
SIEM & SOC Integration
Export your agent security telemetry directly to tools like Splunk, Sentinel, or Datadog. Keep your existing security operations center (SOC) informed of AI-specific threats in real-time.
Mission-Critical Use Cases for AI Agents
Vector enables organizations to transition from passive AI experiments to autonomous production workflows. By providing a secure orchestration layer, Vector ensures that your most powerful AI agents can act with speed and precision without compromising your security posture or regulatory compliance.
Secure Engineering & Dev-Agent Workflows
Govern the use of MCP-enabled development tools like Cursor, Claude Code, and GitHub Copilot. Vector monitors the connection between IDE agents and your source code repositories, preventing the accidental exfiltration of proprietary IP and ensuring that AI-generated code changes adhere to internal security standards.
Autonomous Customer Service & Transactions
Empower support agents to perform real-world actions like processing refunds, modifying account permissions, or updating CRM records. Vector validates the "intent" behind every transaction, ensuring the agent doesn't overstep its authority or get manipulated into performing unauthorized high-value actions.
Financial Intelligence & SQL Guardrails
Safely connect AI agents to sensitive financial databases via MCP. Vector acts as an intelligent proxy for SQL queries and data retrievals, redacting PII in real-time and preventing agents from executing "destructive" commands that could lead to data loss or corruption.
Sales & Marketing Automation (GTM)
Enable agents to autonomously research leads, personalize outreach, and interact with marketing stacks (like Salesforce or HubSpot). Vector protects against "Indirect Prompt Injections" found on external websites, ensuring your GTM agents aren't hijacked by malicious instructions while browsing the web.
Self-Healing IT & Infrastructure Ops
Deploy AI agents for automated system monitoring and troubleshooting. Vector provides the necessary "kill switch" and granular permissioning to ensure that IT agents can restart services or clear logs without gaining "God-mode" access to your entire cloud infrastructure.
Agentic Threat Hunting & SecOps
Utilize autonomous agents to assist your Security Operations Center (SOC) in incident response. Vector monitors these high-privilege agents as they navigate your security stack, providing a human-readable audit trail of every forensic action taken during a threat-hunting mission.
Advanced Action-Layer Inspection Engines
Vector deploys a comprehensive suite of real-time analyzers at the agent gateway to validate tool-calls, MCP resource access, and semantic intent. This ensures every autonomous action is scrutinized for security, privacy, and policy compliance before it reaches your infrastructure.
Frequently Asked Questions
Secure the Autonomous Action Layer
Govern AI agents and MCP connections with intent-based security to prevent unauthorized execution, data exfiltration, and non-compliant behaviors in real-time.